Reimagining
Rule
Rule

When Security Fails, It's Rarely the Camera.
It's the Rules Behind It.
When Security Fails, It's Rarely the Camera.
It's the Rules Behind It.
Business
Business
Business

Certenity
Certenity
The Product
The Product
The Product
Certenity is an enterprise
Certenity is an enterprise
Certenity is an enterprise
AI video analytics SaaS platform.
AI video analytics SaaS platform.
AI video analytics SaaS platform.
It transforms live camera feeds into proactive threat detection.
It transforms live camera feeds into proactive threat detection.
It transforms live camera feeds into proactive threat detection.
Enhances
security across large-scale sites like
Warehouses
Warehouses
Warehouses
campuses
campuses
campuses
retail chains
retail chains
retail chains
industrial facilities
industrial facilities
industrial facilities
Role:
Role:
UX/UI Designer
UX/UI Designer
Duration:
Duration:
3 Months
3 Months
Product focus:
Product focus:
Enterprise UX
Enterprise UX
Deep ownership across:
Deep ownership across:
4/12 modules
4/12 modules
Uncovering User Needs through Research
Uncovering User Needs through Research
We Listened First
We Listened First
Age:
32
City:
Austin
#persona1
#persona1
Operator
Operator

Security Personnel
Jared Smith
Jared Smith
A security professional at a busy storage facility in Austin, monitors multiple cameras to track incidents and respond swiftly. He needs an intuitive system for real-time surveillance and alerts.
A security professional at a busy storage facility in Austin, monitors multiple cameras to track incidents and respond swiftly. He needs an intuitive system for real-time surveillance and alerts.
Pain Points
Pain Points
Frustrated by overly complex or unintuitive surveillance systems that make it challenging to perform essential tasks
Frustrated by overly complex or unintuitive surveillance systems that make it challenging to perform essential tasks
Difficulty in investigating and reviewing video footage in response to reported events or alarms
Difficulty in investigating and reviewing video footage in response to reported events or alarms
Pain Points
Difficulty in assigning access to specific cameras
Difficulty in assigning access to specific cameras
Lack of integration with other security systems
Lack of integration with other security systems
Lack of user-friendly interface
Lack of user-friendly interface
Security Admin
Alex Johnson
Alex Johnson
A security admin, manages access, defines rules, and coordinates teams. He needs a centralized platform to streamline security operations efficiently.
A security admin, manages access, defines rules, and coordinates teams. He needs a centralized platform to streamline security operations efficiently.

Age:
38
City:
Austin
#persona2
#persona2
#persona2
Admin
Admin
I M A G I N E
I M A G I N E
I M A G I N E
Inside an enterprise security operations room, operators monitor hundreds of camera feeds simultaneously. When an AI rule triggers an intrusion, a line crossed, a face recognized then system doesn't wait. It alerts instantly. The operator responds.
Inside an enterprise security operations room, operators monitor hundreds of camera feeds simultaneously. When an AI rule triggers an intrusion, a line crossed, a face recognized then system doesn't wait. It alerts instantly. The operator responds.
Inside an enterprise security operations room, operators monitor hundreds of camera feeds simultaneously. When an AI rule triggers an intrusion, a line crossed, a face recognized then system doesn't wait. It alerts instantly. The operator responds.
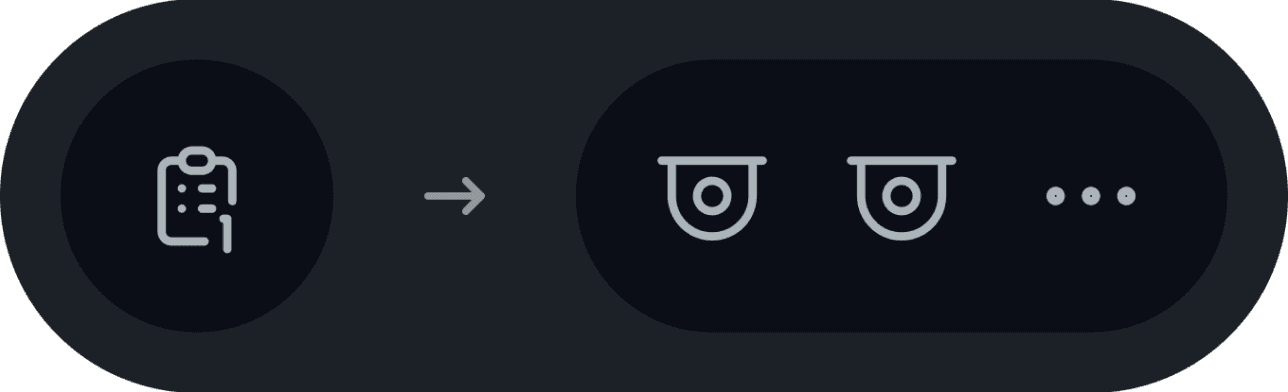
What is a Rule?
What is a Rule?
Without a rule, a camera just records. With one, it understands what to watch for, where to look, and when to act.
Without a rule, a camera just records. With one, it understands what to watch for,
where to look, and when to act.
Without a rule, a camera just records. With one, it understands what to watch for, where to look, and when to act.

A camera feed with no rules applied
A camera feed with no rules applied
A camera feed with no rules applied

The same feed, now actively detecting threats.
The same feed, now actively detecting threats.
The same feed, now actively detecting threats.
That's what Rule Configuration does.
That's what Rule Configuration does.
Rule Configuration is the
Rule Configuration is the
Rule Configuration is the
Admin's control center.
Admin's control center.
Admin's control center.
No Rules = No Detection.
No Rules = No Detection.
No Rules = No Detection.
No Detection = No Security.
No Detection = No Security.
No Detection = No Security.
It is the most operationally critical module in the platform.
It is the most operationally critical module in the platform.
It is the most operationally critical module in the platform.
The Core Tension
Enterprise security runs on scale. A single site can have 50, 100, even 200+ cameras. Each camera needs rules. Each rule needs configuration.
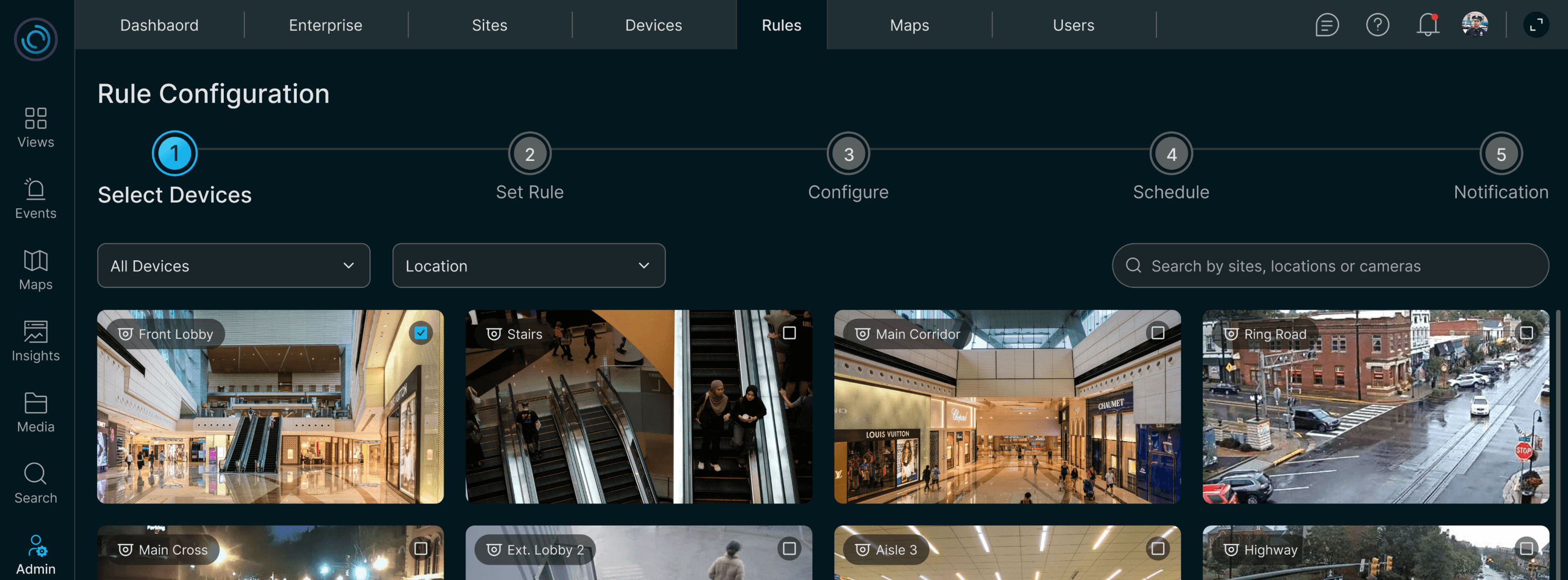
Previous Certenity’s Rule Configuration design
Limited to single devices
Ignoring multi-camera realities in large sites.
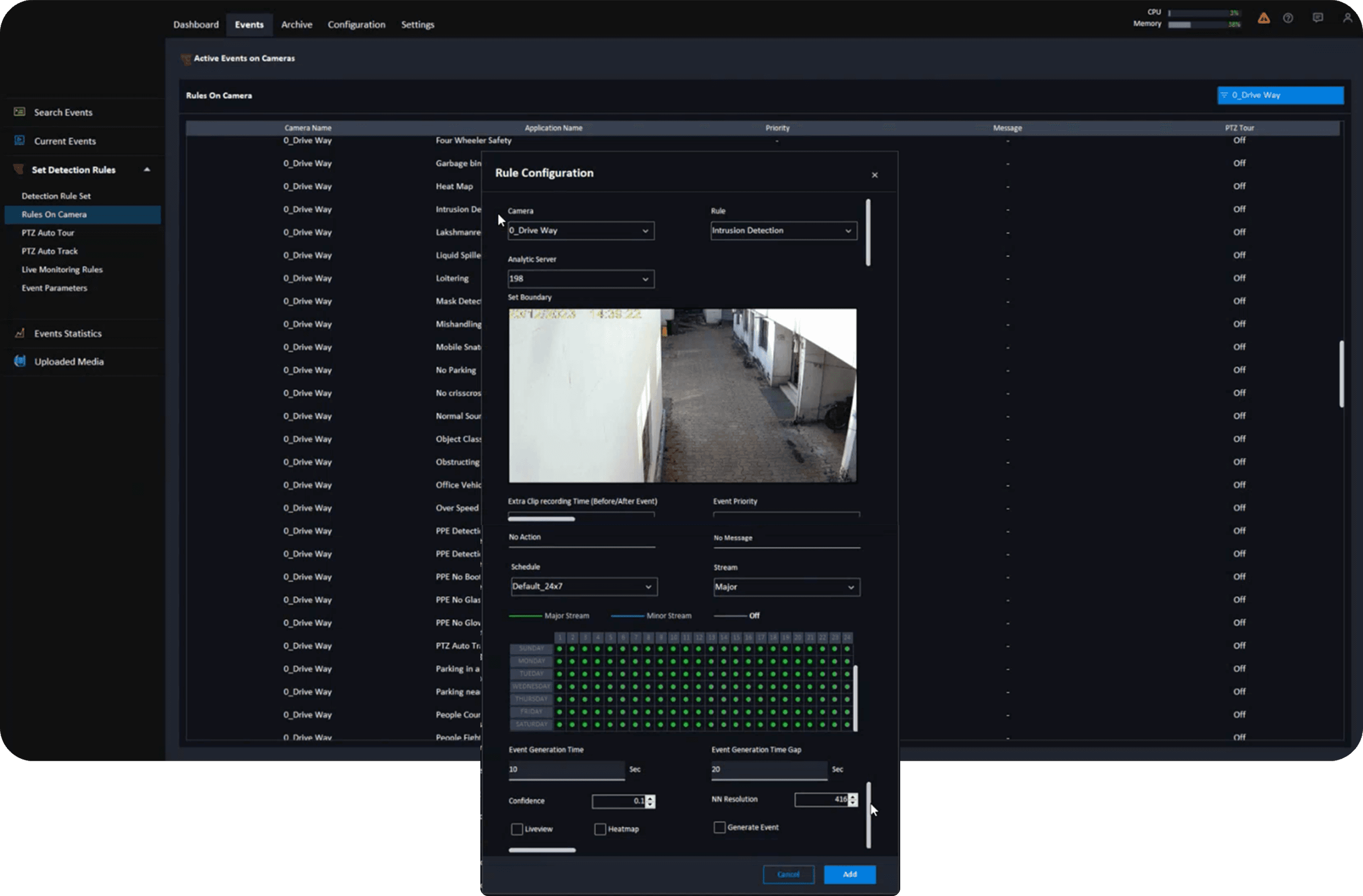
No built-in guidance
Frustrating mixed-skill users (tech-savvy admins vs. on-site operators).
The rule creation flow is
packed into a small, long-scroll popup.
Built for simplicity, not scale.
The
Business
Problem
The
Business
Problem
The platform was growing.
The platform was growing.
More clients. More sites. More cameras.
More clients. More sites. More cameras.
More rule types including premium AI rules that clients had to purchase.
But the configuration tool hadn't grown with it.
More rule types including premium AI rules that clients had to purchase. But the configuration tool hadn't grown with it.
More rule types including premium AI rules that clients had to purchase.
But the configuration tool hadn't grown with it.
1
Admins weren't using advanced rule types, reducing platform value
Admins weren't using advanced rule types, reducing platform value
Admins weren't using advanced rule types, reducing platform value
2
Setup errors were costly. Assigning a rule to the wrong camera could waste a limited premium license
Setup errors were costly. Assigning a rule to the wrong camera could waste a limited premium license
Setup errors were costly. Assigning a rule to the wrong camera could waste a limited premium license
3
That friction silently discouraged admins from using premium rules at all
That friction silently discouraged admins from using premium rules at all
That friction silently discouraged admins from using premium rules at all
The goal wasn't just better UX.
The goal wasn't just better UX.
It was removing the friction that was silently limiting what the platform could do.
It was removing the friction that was silently limiting what the platform could do.
It was removing the friction that was silently limiting what the platform could do.
Four decisions.
Each one shaped the product. Here's what we chose, what we rejected, and why.
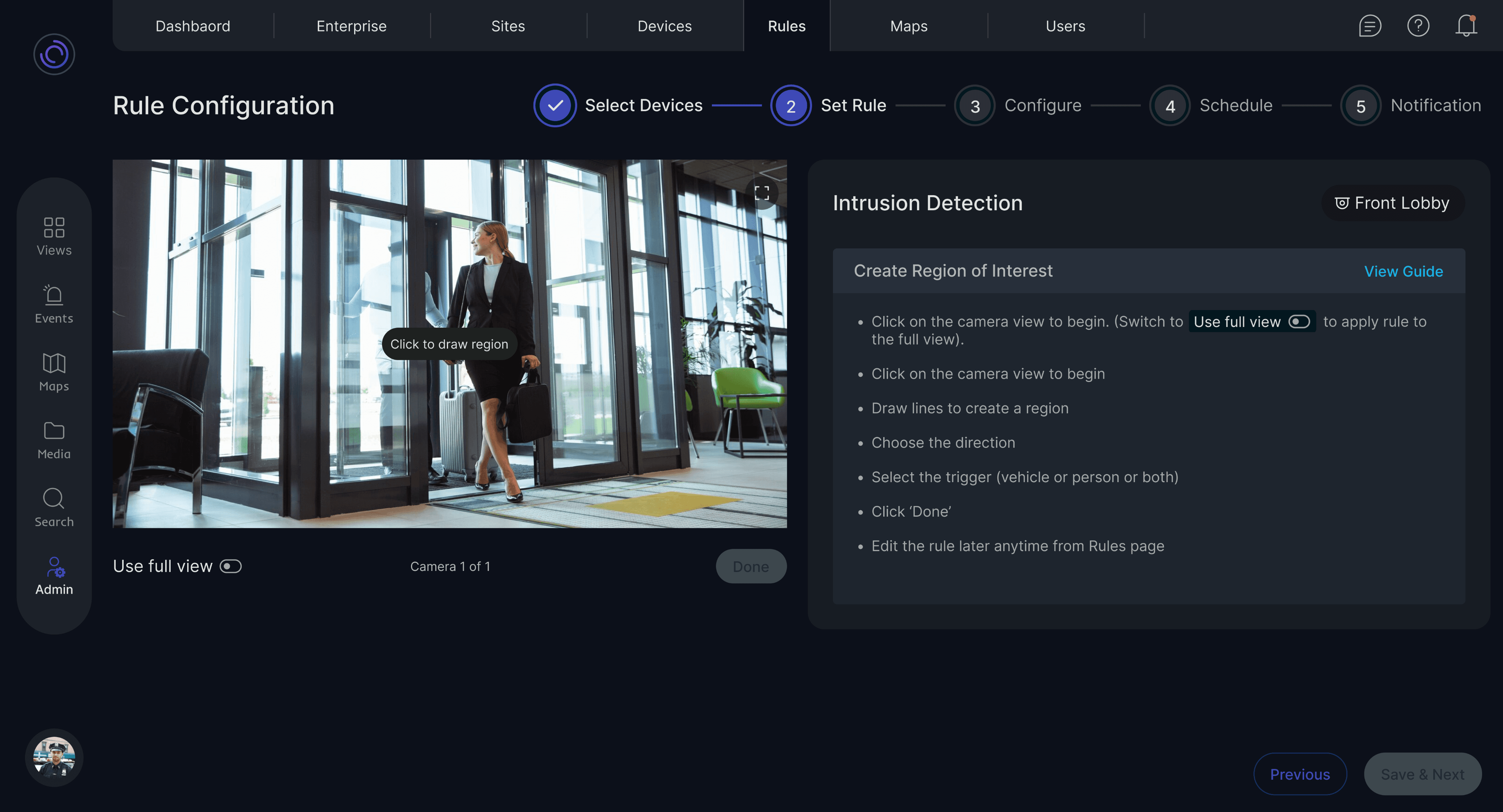
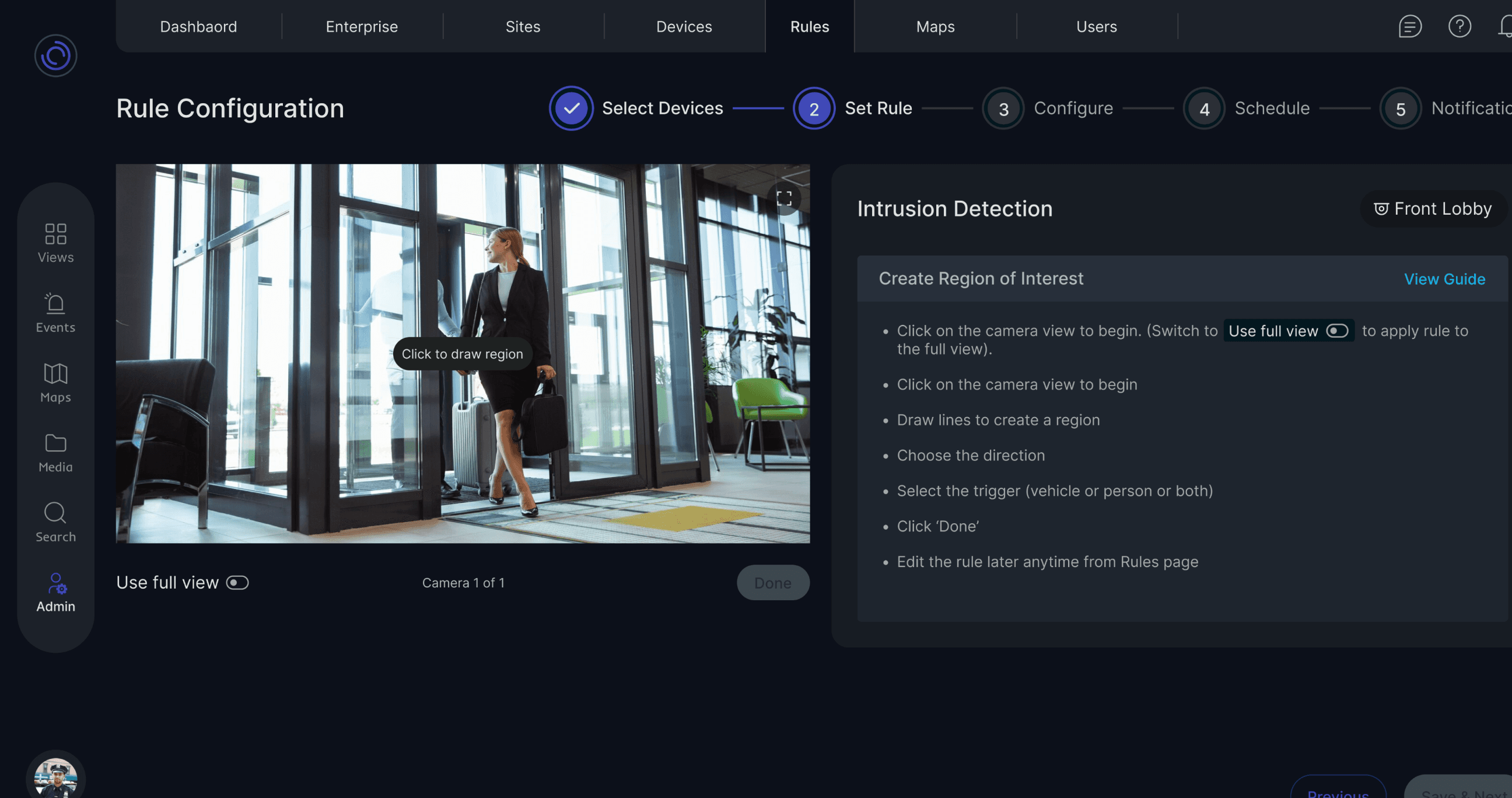
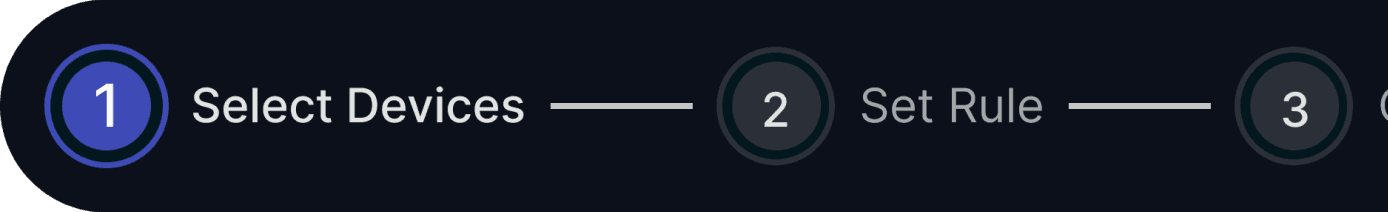
Rule configuration isn't a quick action. It's a deliberate, multi-step process with real operational consequences. It deserved its own space.
Popup to Full Screen
"One-click convenience was costing us clarity."

Many-to-many felt powerful from the top level became an infinite loop the deeper you went.
What we kept:
1-to-1 — One rule, one device. Simple, precise, no ambiguity.
1-to-Many — One rule, multiple devices. Scalable without losing control.
Rejecting Many-to-Many
"More flexibility isn't always more power."
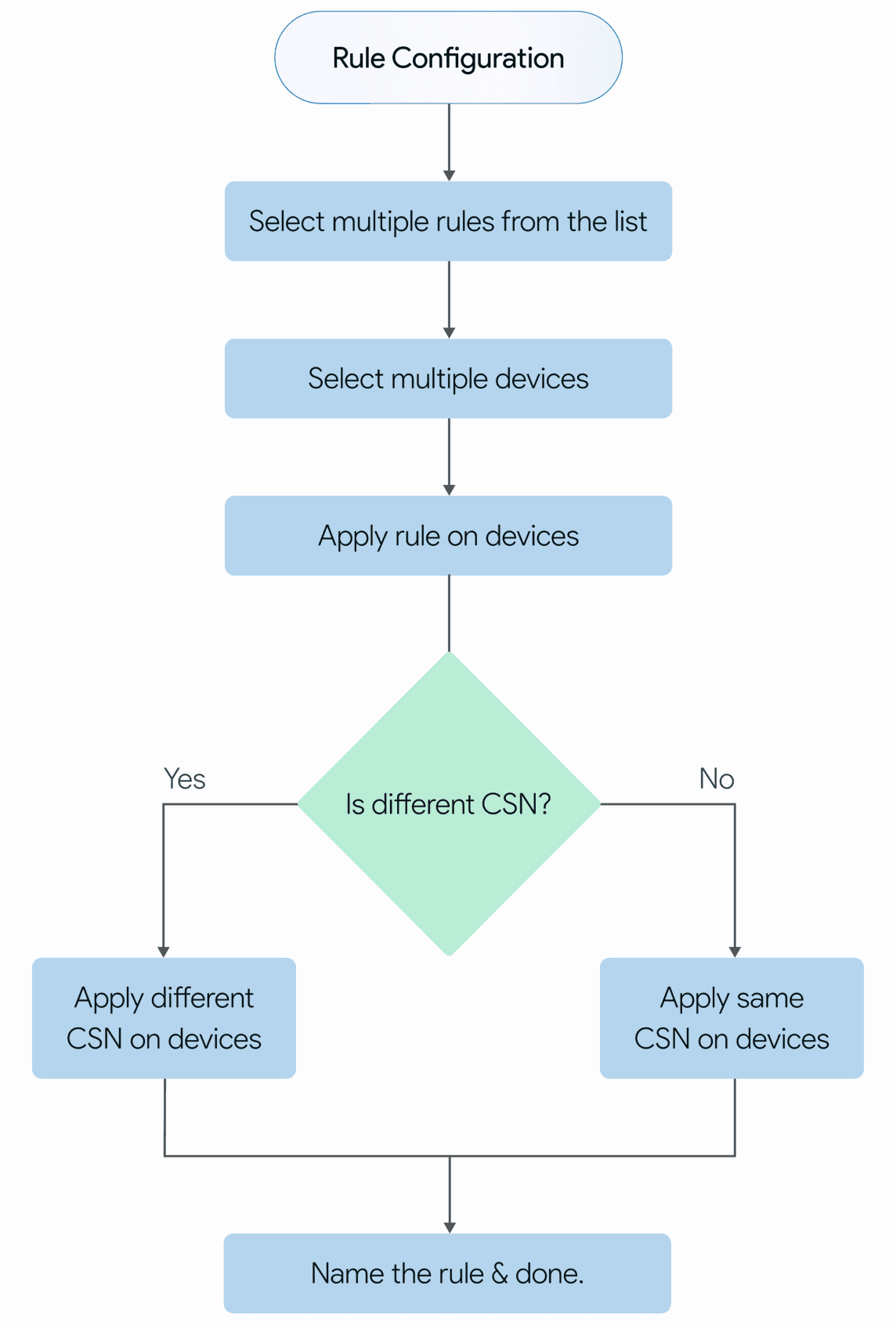
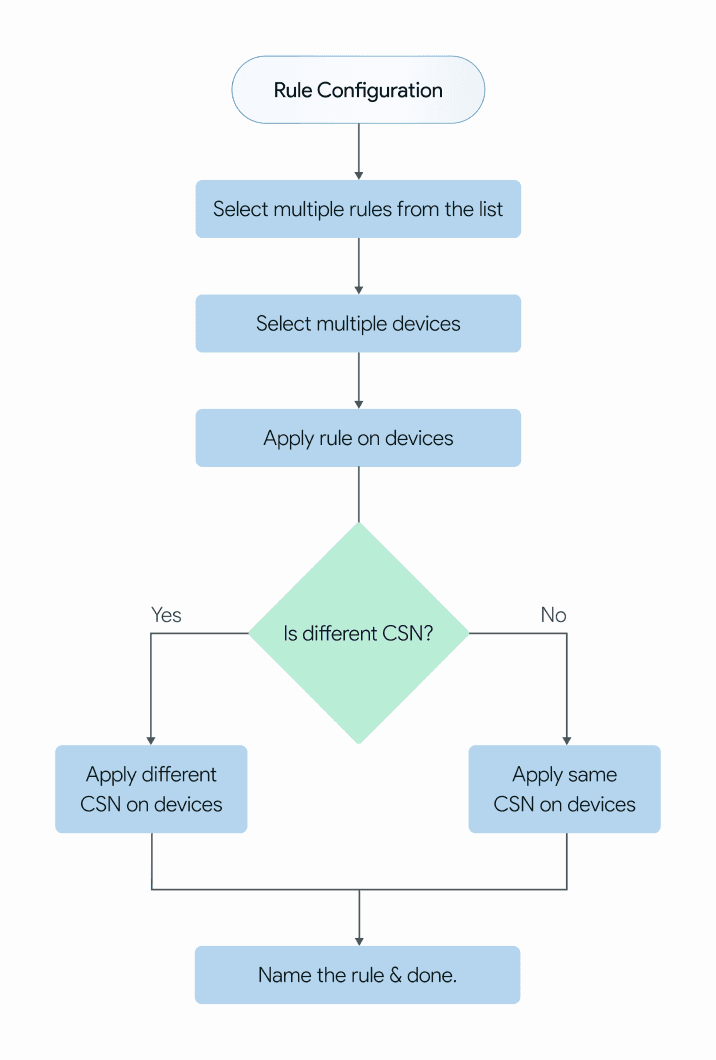
Configure, Schedule, Notification.
Each stage has one job. One mental goal.
The stepper makes it visible, admins always know where they are, what they've completed, and what's next. No guessing.
The CSN Framework
"A rule isn't just a trigger. It's a lifecycle."
Configure
Notification
Schedule
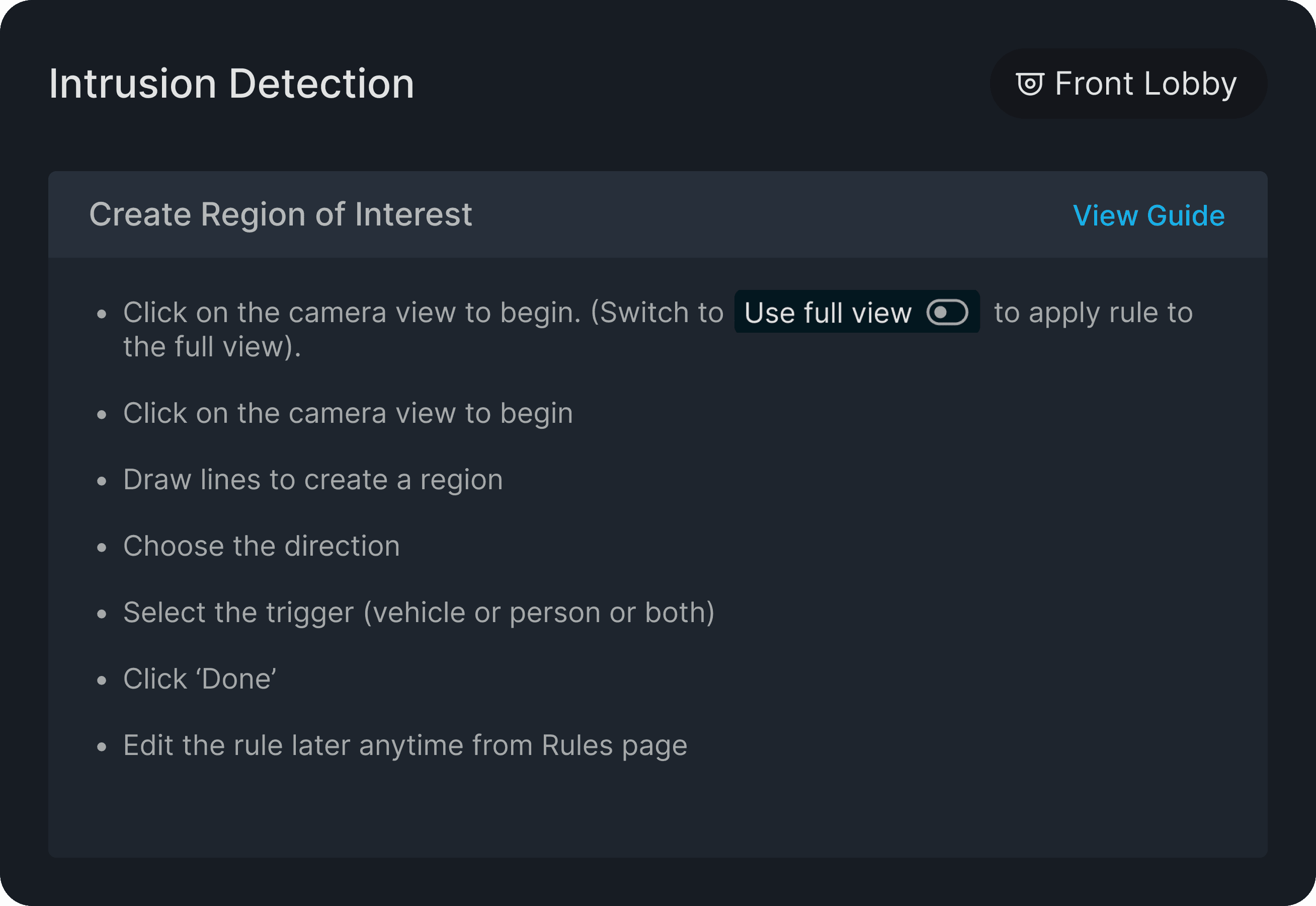
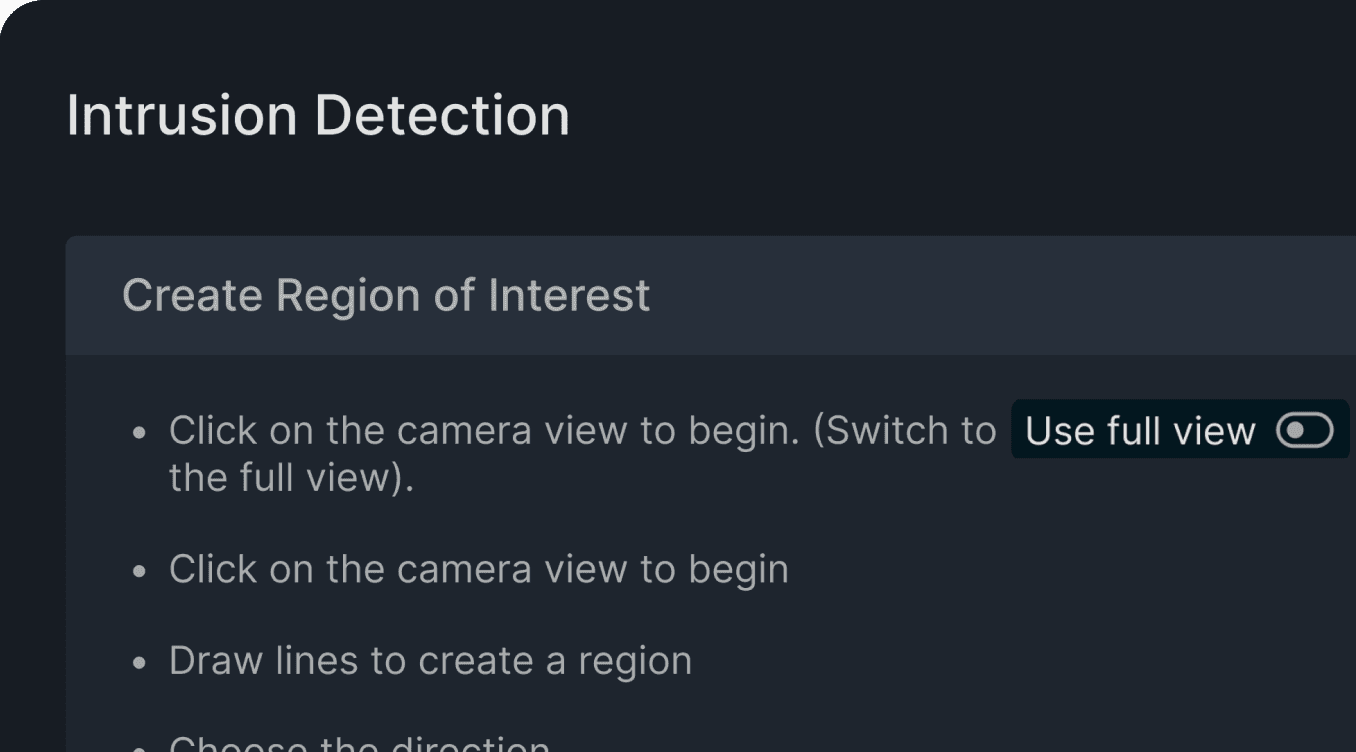
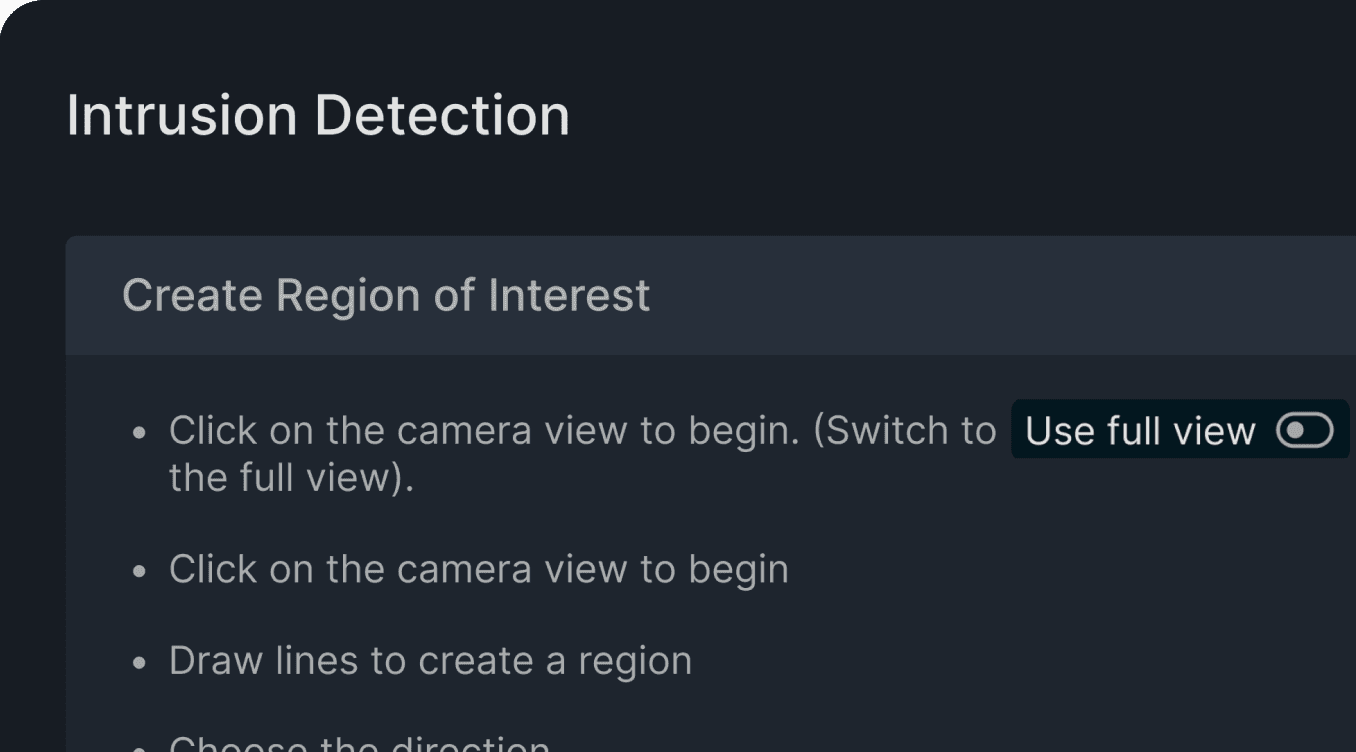
It's a quality control layer embedded into the workflow. Don't assume expertise. Design for the moment when expertise is absent.
Guidance over Knowledge
"An incorrectly drawn zone doesn't just look wrong. It counts wrong."
Four decisions.
Each one shaped the product. Here's what we chose, what we rejected, and why.
Popup to Full Screen
"One-click convenience was costing us clarity."
Rejecting Many-to-Many
"More flexibility isn't always more power."
The CSN Framework
"A rule isn't just a trigger. It's a lifecycle."
Configure
Schedule
Notification
Guidance over Knowledge
"An incorrectly drawn zone doesn't just look wrong. It counts wrong."
Four decisions.
Each one shaped the product. Here's what we chose, what we rejected, and why.
Rule configuration isn't a quick action. It's a deliberate, multi-step process with real operational consequences. It deserved its own space.
Popup to Full Screen
"One-click convenience was costing us clarity."
Many-to-many felt powerful from the top level became an infinite loop the deeper you went.
What we kept:
1-to-1 — One rule, one device. Simple, precise, no ambiguity.
1-to-Many — One rule, multiple devices. Scalable without losing control.
Rejecting Many-to-Many
"More flexibility isn't always more power."
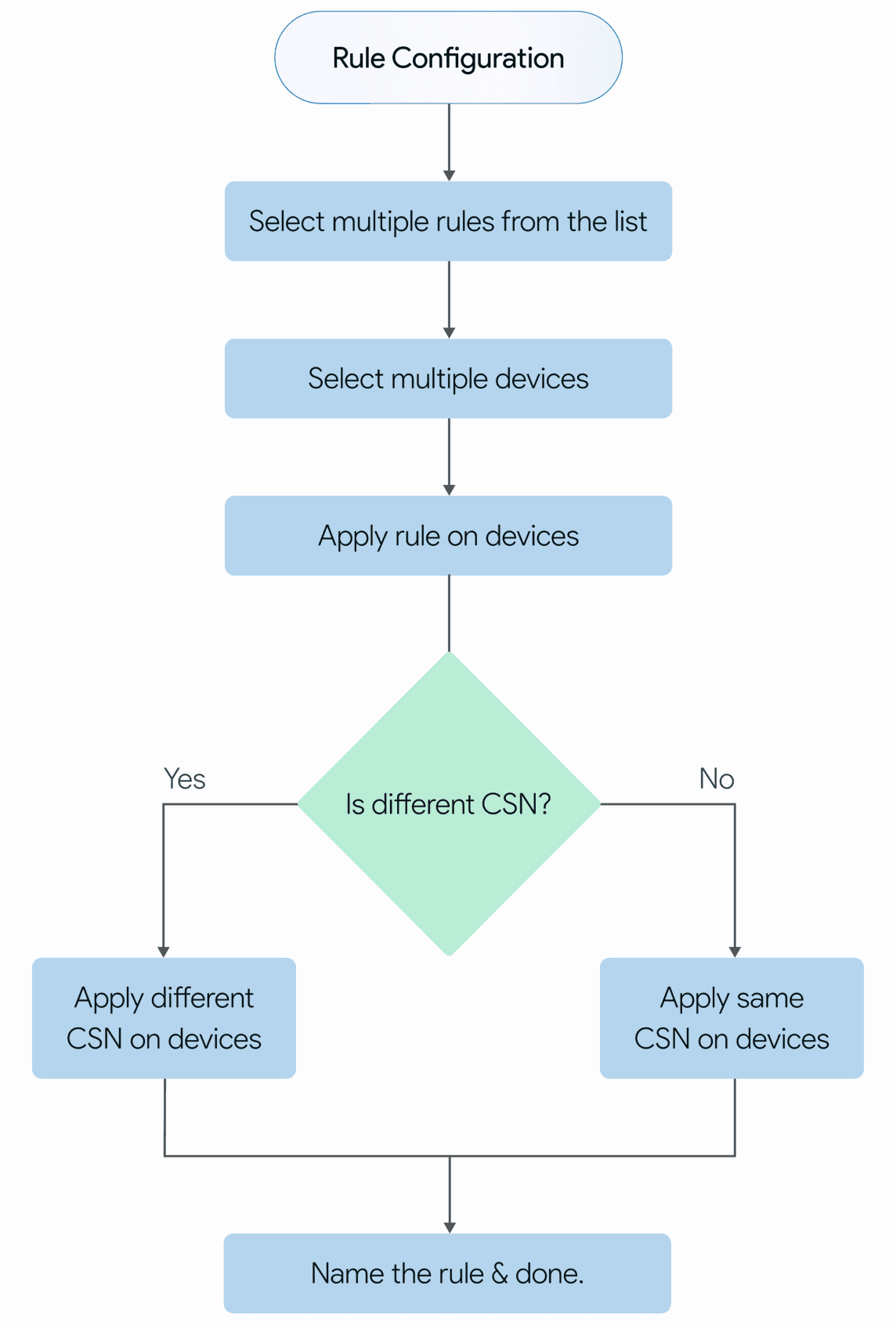
Configure, Schedule, Notification.
Each stage has one job. One mental goal.
The stepper makes it visible, admins always know where they are, what they've completed, and what's next. No guessing.
The CSN Framework
"A rule isn't just a trigger. It's a lifecycle."
Configure
Notification
Schedule
It's a quality control layer embedded into the workflow. Don't assume expertise. Design for the moment when expertise is absent.
Guidance over Knowledge
"An incorrectly drawn zone doesn't just look wrong. It counts wrong."
Solution Highlights
Solution Highlights
Five features. Each one a direct answer to a real problem.
Five features. Each one a direct answer
to a real problem.
Adaptive Configuration Modes
Choose your device,
your way.

Selecting one device (One to One)
Selecting one device (One to One)
Selecting one device (One to One)

Selecting multiple device (One to Many)
Selecting multiple device (One to Many)
Selecting multiple device (One to Many)
Set rule on one device or..
Set rule on one device or..
Set rule on one device or..

..on many devices, effortlessly
..on many devices, effortlessly
..on many devices, effortlessly




A spacious canvas that empowers admins to define rules effortlessly and with precision.
A spacious canvas that empowers admins to define rules effortlessly and with precision.
A spacious canvas that empowers admins to define rules effortlessly and with precision.


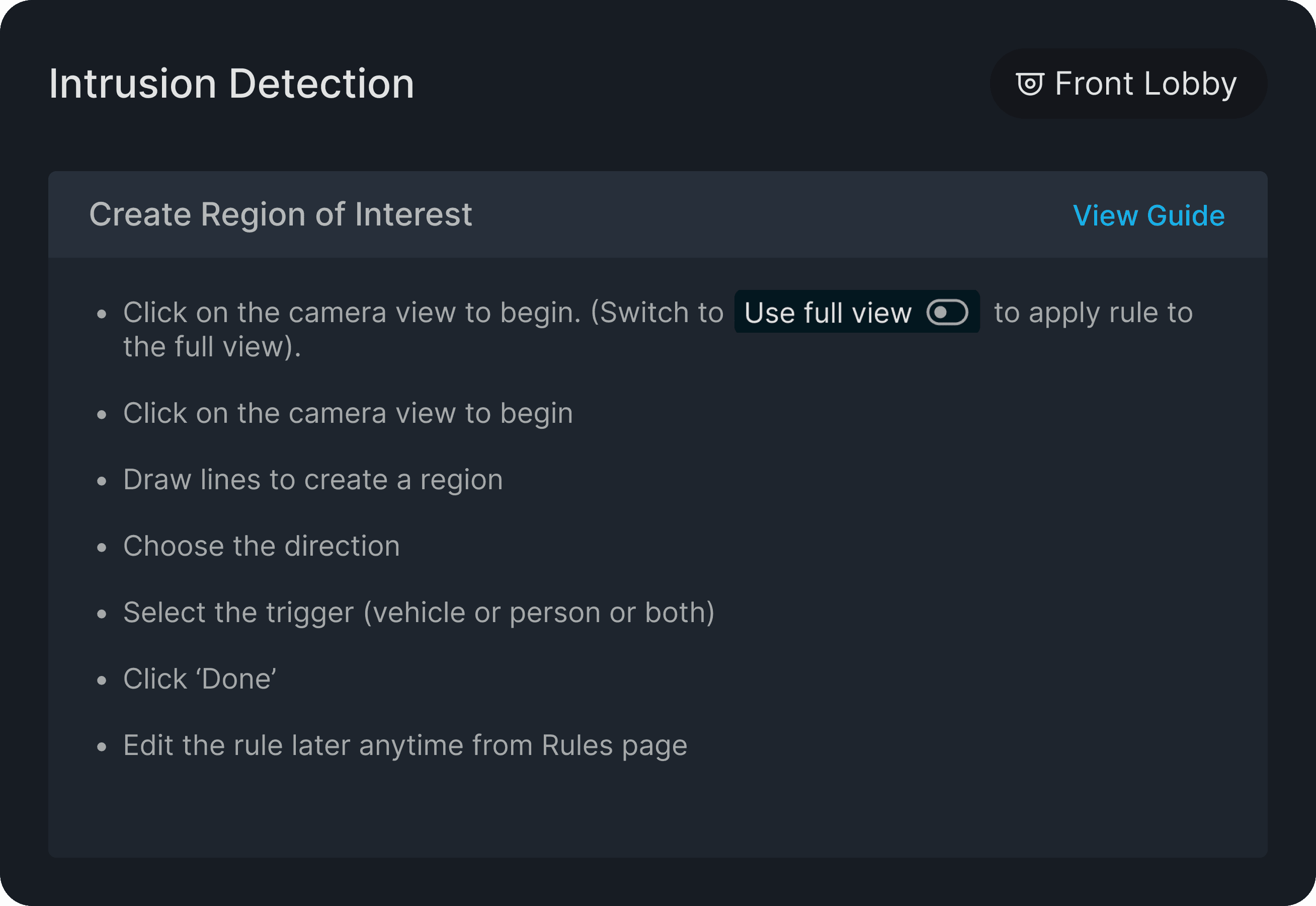
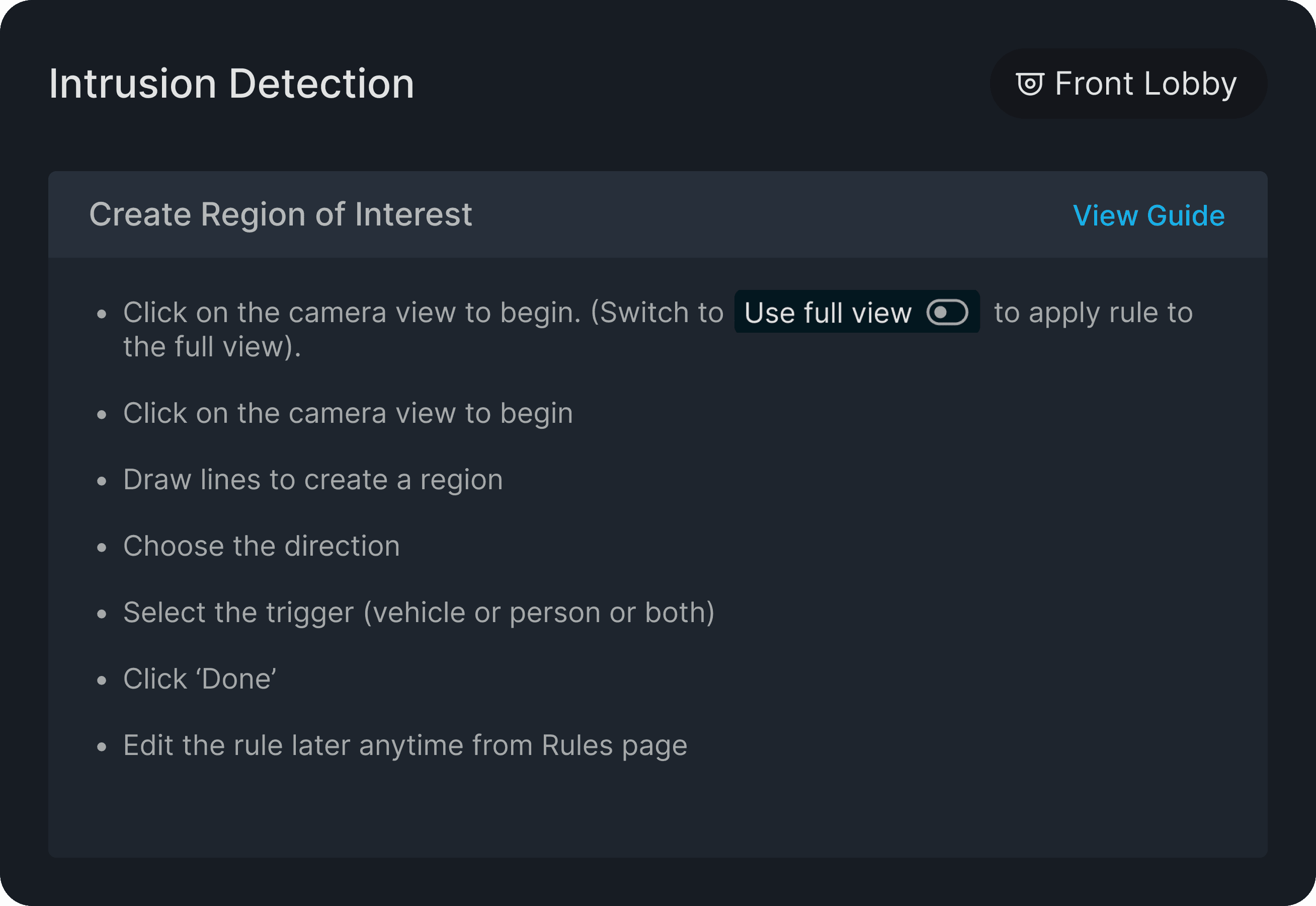
Built-in guidebook with smart Do’s and Don’ts to ensure accurate rule setup.
Built-in guidebook with smart Do’s and Don’ts to ensure accurate rule setup.
Built-in guidebook with smart Do’s and Don’ts to ensure accurate rule setup.
From Logic to Interface:
Visualizing CSN
Configure - Defining the response
Setting what happens when an event triggers.
Schedule - Timing the watch
Notification - Alerting the right eyes

From Logic to Interface:
Visualizing CSN
Configure - Defining the response
Setting what happens when an event triggers.
Schedule - Timing the watch
Notification - Alerting the right eyes
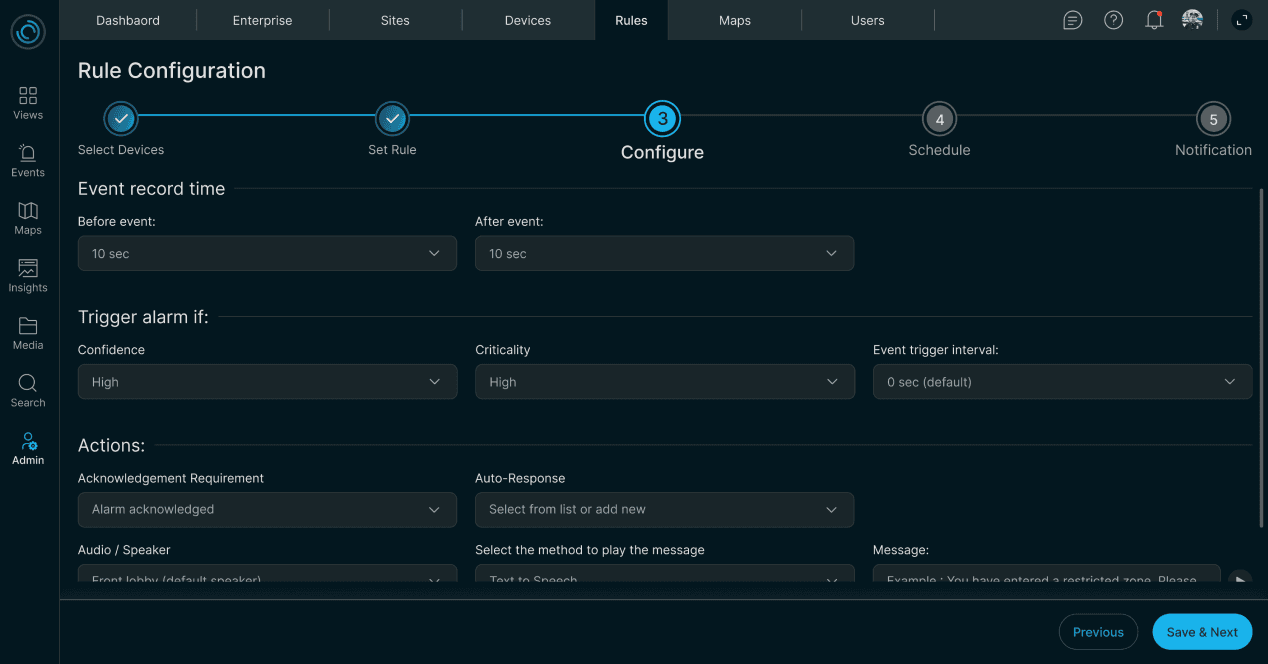
From Logic to Interface:
Visualizing CSN
Defining the response
Setting what happens when an event triggers.
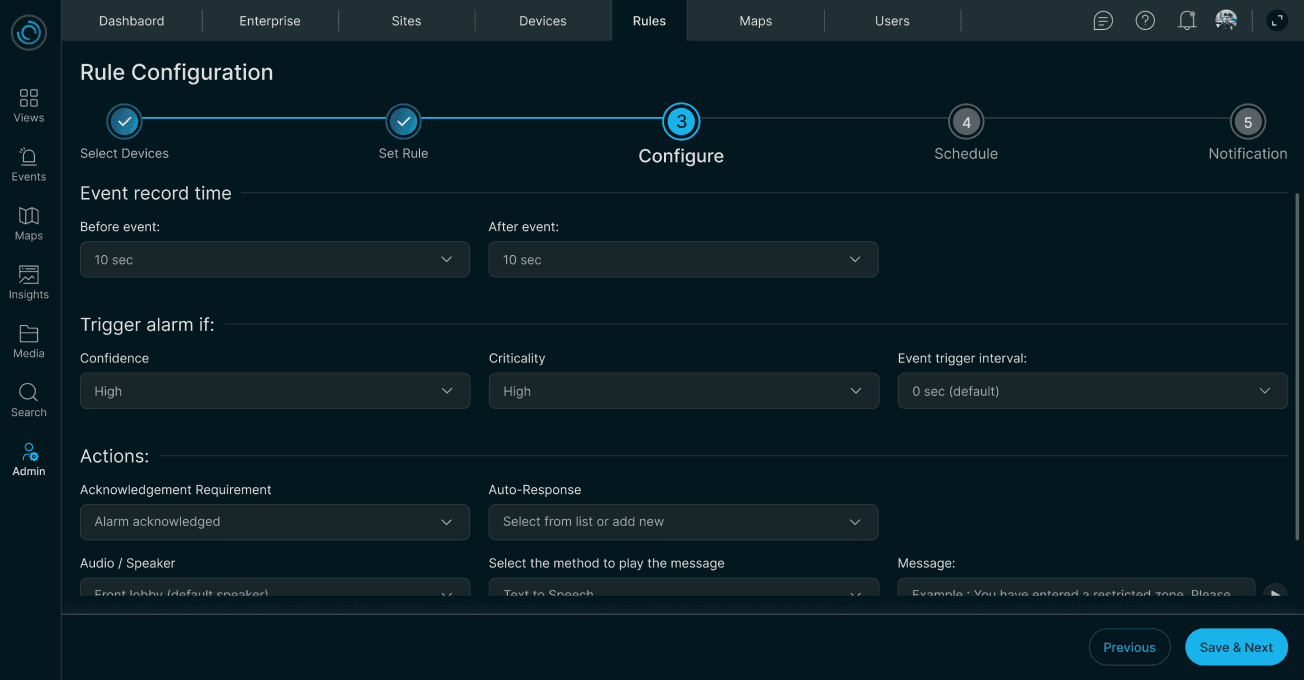
Timing the watch
Setting what happens when an event triggers.

Alerting the right eyes
Deciding who gets notified instantly.

Configure
Schedule
Notification
Estimated Design Impact
Estimated Design Impact
Based on structural changes, not measured data
Based on structural changes, not measured data

Single endless form →
6 structured steps
Single endless form →
6 structured steps
Single endless form →
6 structured steps
Estimated 40–50% reduction in setup time
Estimated 40–50% reduction in setup time
1-to-1 only →
1-to-Many mode
1-to-1 only →
1-to-Many mode
1-to-1 only →
1-to-Many mode
One session now covers what previously took many.
One session now covers what previously took many.
Zero guidance →
Contextual guidebook per rule
Zero guidance →
Contextual guidebook per rule
Zero guidance →
Contextual guidebook per rule
Measurable reduction in misconfiguration risk
Measurable reduction in misconfiguration risk
*
These are design intent estimates, not tracked metrics. The platform was not instrumented for usage analytics at this stage.
These are design intent estimates, not tracked metrics. The platform was not instrumented for usage analytics at this stage.




What’s Next..
What’s Next..

System will suggest rules by analyzing device feeds, tailored to the selected rule type.
System will suggest rules by analyzing device feeds, tailored to the selected rule type.
Simplify the entire rule creation into two steps — just prompt and confirm.
Simplify the entire rule creation into two steps — just prompt and confirm.
The Core Tension
Enterprise security runs on scale. A single site can have 50, 100, even 200+ cameras. Each camera needs rules. Each rule needs configuration.
Previous Certenity’s Rule Configuration design
Limited to single devices
No built-in guidance
Packed into a small, long-scroll popup.
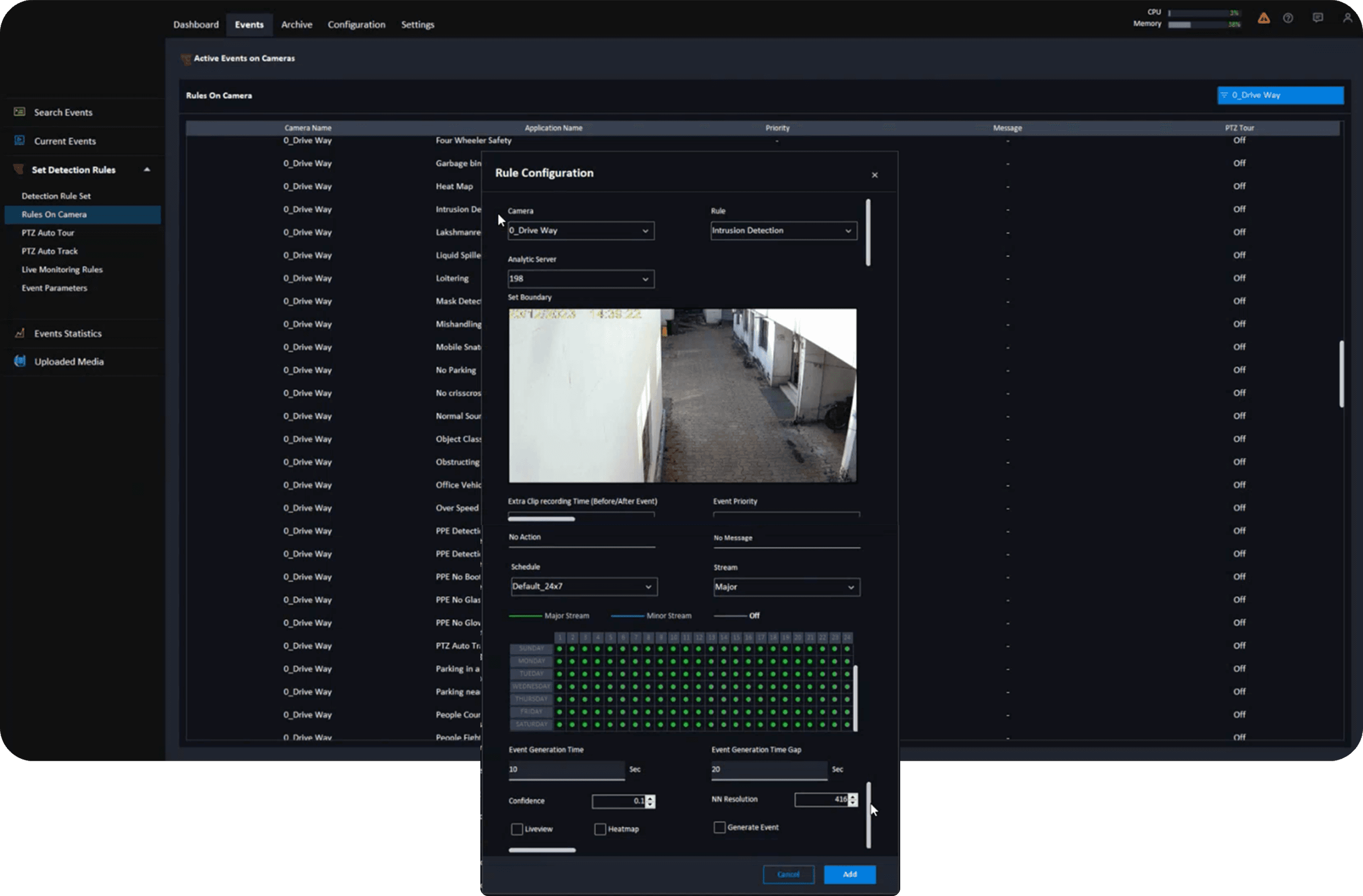
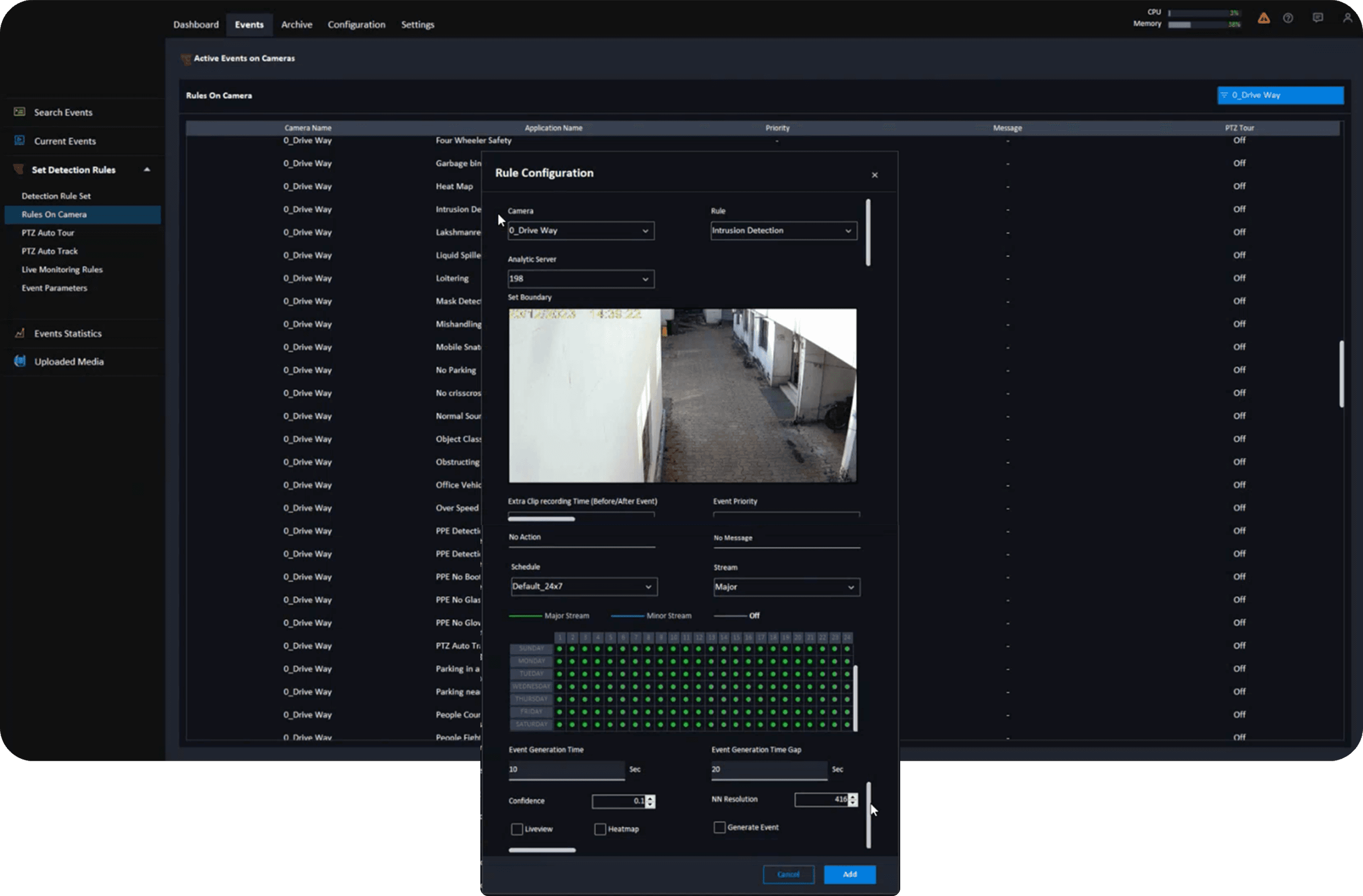
Built for simplicity, not scale.
The Core Tension
Enterprise security runs on scale. A single site can have 50, 100, even 200+ cameras. Each camera needs rules. Each rule needs configuration.
Previous Certenity’s Rule Configuration design
Limited to single devices
Ignoring multi-camera realities in large sites.
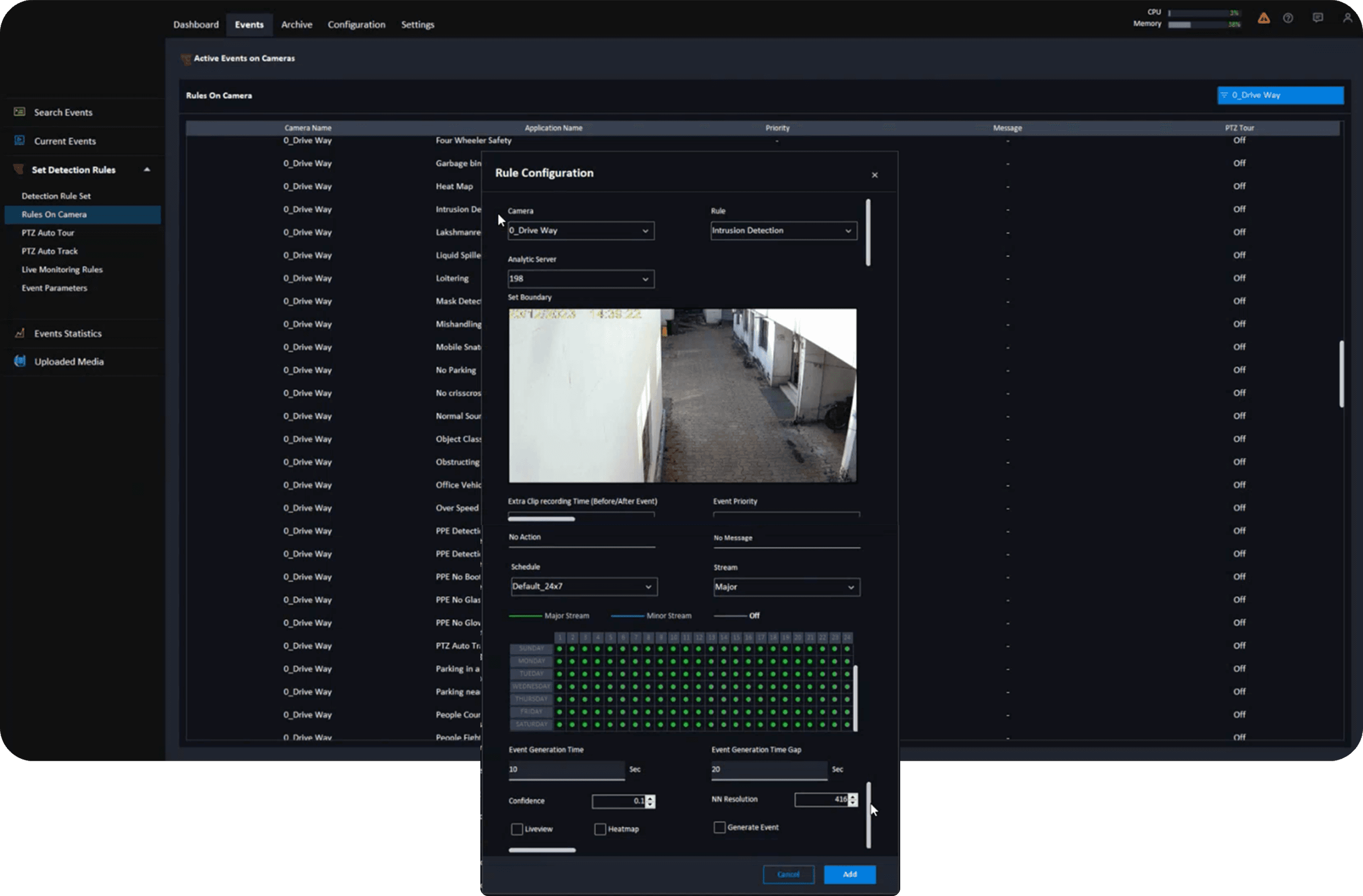
No built-in guidance
Frustrating mixed-skill users (tech-savvy admins vs. on-site operators).
The rule creation flow is
packed into a small, long-scroll popup.
Built for simplicity, not scale.
